Imagine you’re about to send a critical message to your boss. A message with sensitive and private information that must remain secure. In this digital age, a private key becomes your virtual guardian, a crucial alphanumeric code that acts as the gatekeeper to safeguard your message.
Private keys are indispensable, serving as digital signatures that validate ownership and authorize transactions. This article delves into the topic of private keys while also touching upon public keys and seed phrases, all crucial for protecting your cryptocurrency and vital information.
What is a private key?
Typically, all crypto wallets generate private keys. This is the case whether it is a hot or cold wallet, custodial or non-custodial. Importantly, the wallet manufacturer doesn’t provide the key; your device generates it independently. This process is crucial for ensuring security and eliminates the need to trust third parties.
A private key takes the form of a 256-bit generated code of numbers. The randomness of this number is essential to its security; attempting to create one manually would be futile.
Typically, a private key looks like a complex string of numbers, making it impractical for everyday use. Here’s an example in binary form, though the actual one is significantly longer than what we can display here.
Private key in decimal: 8,961,234,765,667,128,953,278,764,293,008,692,816
Other forms include:
- 256-character long binary code
- 64 digit hexadecimal code
- QR code
- Mnemonic phrase
Regardless of its form, this astronomical number is the key to controlling and transferring bitcoin. Storing and safeguarding such a lengthy binary number can be challenging, so wallets provide a more user-friendly solution.
Your private key is a unique secret code validating wallet ownership and facilitating transactions. Note that losing it means permanent inaccessibility to your assets due to the blockchain’s immutable nature. Hence, diligent management and security of this key are vital to protect your digital wealth.
Your private key is a unique secret code validating wallet ownership and facilitating transactions. Note that losing it means permanent inaccessibility to your assets. Hence, diligent management and security of this key are vital to protect your digital wealth.
Recovery seed
Wallets generate a recovery seed to address the issue of memorizing or storing a binary private key. This recovery seed comprises 12 to 24 chosen words. Wallet providers select these words from a standardized list known as the BIP 39-word list to ensure compatibility.

Here’s how the process works:
- It’s divided into groups of 11 binary digits.
- Each group is converted to a decimal number.
- The BIP 39 word list is used to find the corresponding word for each decimal number.
- These words, in a specific order, become your recovery seed.
This recovery seed is the key to your crypto ownership. If you possess these words in the correct sequence, you have the power to control your crypto holdings. Seed phrases can be either custom-made or randomly generated by the wallet itself.
Protecting your recovery seed
Never share it online, take pictures of it, or upload it to the cloud. Malicious actors constantly scour the internet for exposed recovery seeds, as possessing them equates to control over your crypto asset. Always store your recovery seed in a secure and offline location, away from potential threats.
Advantages of private keys
- Enhanced security: Longer and more random sequences boost resistance to breaches and attacks, elevating overall protection.
- Efficiency: Private keys use symmetric key encryption, making them quick and reliable
- Improved performance: Encryption algorithms are simpler to implement and facilitate faster encryption and decryption of larger data blocks than their public counterparts.
- Efficient resource usage: Symmetric encryption consumes fewer computer resources than public-key encryption.
- Enhanced message security: A unique secret key for each communication pair minimizes the risk of a broad message security breach. If a key is compromised, only the messages between the specific sender and recipient are affected, ensuring the security of others’ communications.
Data integrity: Private key encryption safeguards data integrity through mechanisms like message digests and hashing, effectively detecting any alterations or tampering that may occur during transmission.
Disadvantages of private keys
- Insecure key exchange: Utilizing insecure methods to transmit encryption keys may grant third parties access to critical data, raising concerns about the message’s origin and legitimacy.
- Key proliferation: Managing multiple private keys can become inconvenient when segregating data or assets into distinct groups, potentially leading to security risks when sharing keys with different parties.
- Irrevocable signatures: Encryption cannot provide irrevocable digital signatures, posing challenges when dealing with disputes or uncertainties.
- Key management: Effectively managing encryption keys is crucial to safeguard them against loss, compromise, or unauthorized access.
To bolster security, it’s crucial to frequently change encryption protocols for sensitive data, reducing vulnerabilities due to leaks or theft.
How do they work?
Cryptocurrency transactions rely on digital keys and addresses to manage ownership and access to virtual tokens. While anyone can deposit bitcoin or other tokens into a public address, only the holder of the specific private key can retrieve them. Private keys typically appear as alphanumeric strings to simplify their use and protection.
Creating a public address is straightforward, but reversing the process to generate a private key from a public one is extremely challenging due to advanced encryption methods. You can liken this concept to files locked with a unique key. Just as anyone can place items inside the safe, only the individual with the key can access its contents, emphasizing the importance of safeguarding the key to prevent unauthorized access.
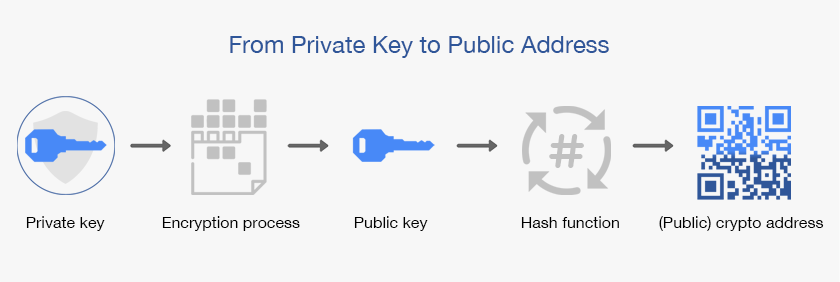
The role of public keys
While private keys are essential for controlling bitcoin, public keys play a vital role in the cryptocurrency ecosystem. A public key is derived from the private key and is used to generate crypto addresses. These addresses are safe to share with others, as they only allow individuals to send crypto to you, not take it.
A crypto address is what you provide to others to receive cryptocurrency. It can be displayed as a QR code for easy scanning. Each address is tied to a public key, and the blockchain records the associated asset transactions.
Public keys vs. private keys
Private keys and public keys perform very different functions. Both are necessary to ensure crypto transactions are conducted securely. These keys usually take the form of lengthy strings of alphanumeric characters, which are cryptographically linked, meaning any transaction encrypted by a public key can only be decrypted using its corresponding private key. This encryption method is known as “asymmetric-key cryptography”.
Additionally, public keys play the role of facilitating incoming transactions into your wallet. In contrast, private keys act as gatekeepers, verifying these transactions and confirming your ownership of a specific wallet address. Public keys are typically shared openly, but private keys must be safeguarded as top-secret information.
Generating a private key
Mobile and desktop wallets typically automate the generation of a private key, but they may offer the choice to create a wallet with your own private key manually.

However, if you want to generate one for heightened assurance, you can use the secrets module in Python to generate a private key. This key generation method is highly secure and difficult to replicate, even with access to the same computer.
Additionally, you can use a commonly known algorithm called RSA or Rivest–Shamir–Adleman. The private key represents two large prime numbers generated in the algorithm, and the product of these prime numbers is then used to generate the public key. Additionally, you can use sites, including random.org and bitaddress.org, a service for generating random bytes to create private keys.
How do you store a private key?
Much like locking valuable documents in a secure safe, it’s important to prioritize the protection of your private keys. These keys should be stored securely in an offline location. There are several methods to achieve this; some investors choose to store their private keys on an offline computer, inscribe them on physical paper, or commit them to memory.
“Backup your seed phrase: Write down your recovery seed phrase on a physical piece of paper and store it in a secure location. This is crucial for wallet recovery if you ever lose access.”
@Eddynathy2: Twitter
For degens engaged in activities such as trading, a software wallet may suffice for casual involvement. However, traders should not keep all of their crypto in hot wallets. Instead, keep the majority in cold storage and hold a certain amount in a hot wallet for trading purposes.
A hardware wallet is crucial for anyone entrenched in the cryptocurrency ecosystem, for example, someone who actively participates in mining operations or has a significant financial stake in the crypto market.
Examples include both Ledge and Trezor wallets. These devices resemble flash drives and employ mnemonic phrases or seed words to generate private and public keys.
Protecting your private key
Protecting your blockchain wallet’s private keys is essential for safeguarding digital assets. To achieve this, follow key protection best practices like creating strong passwords, using two-factor authentication, and regularly backing up wallet data. You can also use random passphrases, also known as seed extensions or extension phrases, to provide an extra layer of security. These passphrases function as a form of two-factor authentication and must be entered each time you access your wallet.
Furthermore, ensure physical and digital security, update software, and encrypt your PC’s hard drive. Consider multi-signature wallets, dedicated hardware devices, and hardware security modules for advanced security.
For recovery and contingency planning, devise a documented process, inform trusted parties, and routinely update for evolving security measures and assets. Remember to stay vigilant and prepared for uncertainties in the crypto space.
Navigating a lost private key scenario
Losing your private key can have profound consequences, particularly with assets like bitcoin. Think of your private key as the exclusive access code to your digital wealth, and when it’s lost, it’s akin to misplacing the only key to your financial vault. In this digital landscape, there is no central authority or customer support to assist in key recovery. Therefore, the responsibility for securing and managing your private key falls squarely on your shoulders.
The role of private keys in crypto security
Private keys play a primary role in bolstering the security of crypto networks. They are the exclusive means to authorize withdrawals and transactions, making them indispensable for cryptocurrency users. Conversely, compromising one’s private key places one’s digital assets at a heightened risk of malicious appropriation. Hence, ensure you safeguard your private key securely, avoiding sharing it online, capturing images of it, or uploading it to any cloud service.
Frequently asked questions
What is a private key in crypto?
How do I get my crypto private key?
What is private and public key crypto?
Is the wallet ID the same as the private key?
How do private keys work?
Where do I find a private key?
Trusted
Disclaimer
In line with the Trust Project guidelines, the educational content on this website is offered in good faith and for general information purposes only. BeInCrypto prioritizes providing high-quality information, taking the time to research and create informative content for readers. While partners may reward the company with commissions for placements in articles, these commissions do not influence the unbiased, honest, and helpful content creation process. Any action taken by the reader based on this information is strictly at their own risk. Please note that our Terms and Conditions, Privacy Policy, and Disclaimers have been updated.




